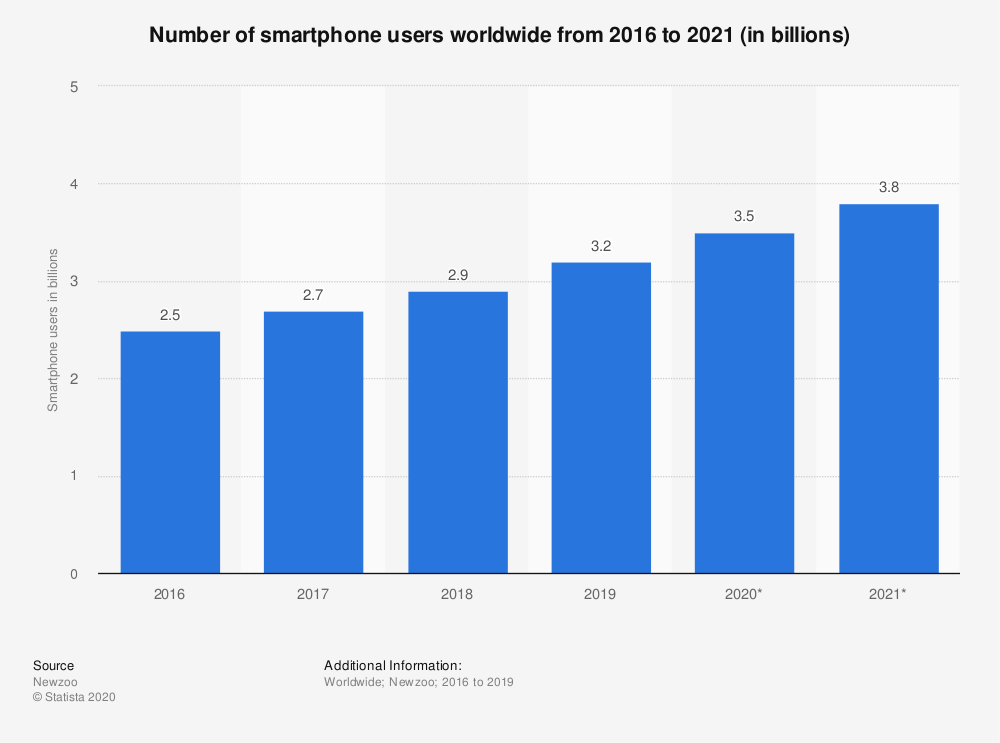
In the recent past, phone hacking has reared its head once again. Needless to say, with the widespread use of smartphones – over 3 billion users worldwide and growing (image below), it is no wonder that hackers are now more focused on hacking smartphones.
Vital services such as banking, online payments, and email that can be accessed on smartphones have revolutionized phone hacking.
Moreover, at least 20% of Android devices are powered by outdated software, as shown in the image below.

Phone hacking is not preserved for Android. iOS users also have their share of hacking to worry about. Earlier this year, the iPhone Camera was hacked as a result of an attack chain that involved 7 bugs.
In this article, we explore hacking – what it is, what users do to make it easier for hacking to happen
What is phone hacking?
Before we get lost in the numbers around devices and how hackers are now more focused on smartphones, let’s ensure that we are on the same page when we talk about phone hacking.
Phone hacking can simply be defined as forced (and unauthorized) access to another person’s phone or the communications thereof.
Why are phones hacked?
Usually, for an action to qualify as hacking, there needs to be a malicious motive, for example:
- Compromising a device’s integrity.
- Defrauding the device’s user or owner.
- Sending spam or commands from an infected device in order to infect other devices or networks.
- Transmission of personal data or credentials without consent or adequate disclosure.
Who is most likely to hack your phone?
Government institutions and hackers top the list of people who are likely to hack into your phones though spouses and employers have joined the list. However, people close to you and online terrorists are likely to hack into your phone compared to the government.
How is your phone hacked?
According to a McAfee Report, hidden apps, are what deliver malware in mobile devices. Since the hidden apps do not have an icon on the home screen, they are able to infect and take over your device without being noticed. The main sources of malware are usually phishing sites, fake apps, and unofficial app stores.
Here are the common ways your phone gets hacked:
- Fraudulent adverts, called maladvertising.
- Apps that seem legit but are fake. These usually have fake reviews on the app store. These fake reviews result in users downloading low-quality apps. The apps also result in fraudulent ad revenue. They request for traffic from control servers to simulate clicks. Ads may be displayed to the user, even if they are irrelevant. Some are requested but not shown to the user, which results in a user’s memory and processing capacity being misused, without their knowledge.
- Fake security updates and notifications. You may receive like the one in the image below:
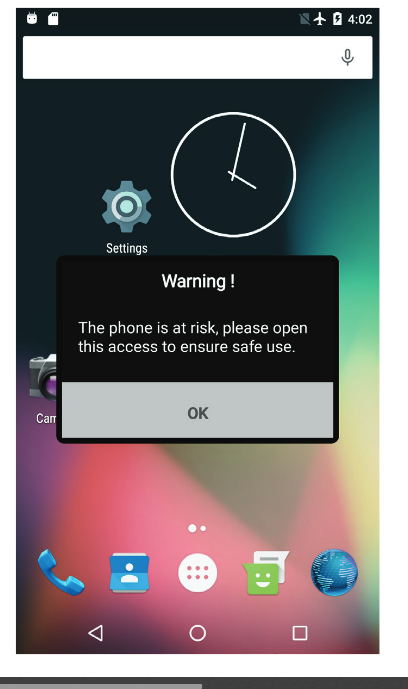
Such notifications when clicked allow full access to the malware’s capabilities. They also do not show any shortcuts or icons.
4. Malware abusing functionalities that run in the background, for example, voice search. The malware installs apps without your knowledge, and usually will not have options for permissions.
A brief overview of Malware
Malware is the main culprit of phone hacking. Anti-Virus Guard (AVG) Technologies describes malware as a software that is created with the sole purpose of obtaining data and damaging the targeted device. The common types of malware are viruses, adware, spyware, worms, ransomware, and Trojan.
How do you tell whether your phone has been hacked?
Here are some of the ways you can tell your phone has been hacked. If you see any of these ‘symptoms’, do investigate further before solely concluding that your phone has actually been hacked.
Short battery life
According to Josh Galindo, the Director of Training at uBreakiFix, mobile phones have a lifespan that is measured in charge cycles. This means when a battery charge cycle is spent the phone will start losing its prowess to retain the charge for long. However, phone hacking has also been attributed to the battery’s short lifespan. Malware installed in your phone could be operating in the background by obtaining data and sending it to the hackers hence draining your battery.
High data usage
High data consumption has puzzled many mobile users. Despite managing their data usage, the cost of using the internet still remains high. Apps running on the background could be the reason as to why you have a high data bill. These apps keep on running without your knowledge and sending the data collected back to the servers.
Receiving anonymous calls and texts
Mobile users should be cautious when they receive anonymous calls especially those with codes not from their countries (as in the Tweet screenshots below). These could be cyber terrorists tricking you into premium-rate numbers in their respective countries. If you fall into the trap you will be charged for the expensive call rates in the hackers’ country.
Your smartphone is slower
There are different reasons why your phone is slowing down and being hacked could be one of them. When efforts to close down running apps don’t resolve the slowness problem, there might be malware running in the background that clashes with the legit applications causing your phone to slow down. If this problem is not solved in time, your device might keep on restarting or crash completely.
Popups
When adware infects your device, there will be an increased number of ads popping up on your screen. As aforementioned, fake virus alerts are one of the ways to get hacked. Once the user clicks on the popup, malware will be downloaded on to their phones.
The way forward? Protect your phone from hackers
Here are some ways you can make it harder for hackers to hack your phone:
Use iVerify

Apple doesn’t tolerate any anti-virus app on the App Store but the approval of iVerify into the App Store is a sigh of relief to iPhones users. It’s an anti-hacking scanner that detects any malware and advises the user on the best solution. The app also helps iPhone users to lock their devices against attacks from hackers.
Avoid public Wi-Fi
Online hackers and scammers use open Wi-Fi to prey on their targets. Mobile users are advised to always turn off their Wi-Fi when not using to avoid falling into such traps. The common places where hackers set free Wi-Fi include restaurants, malls and airports.
Keep your phone number private
The more you share your phone number, the higher the chances of it landing in the hands of scammers. When scammers have your phone number they will start texting you malicious links that might help them obtain your private data.
Update your operating system and apps
After ensuring that the notification to update is actually legit, go ahead and ensure that your Operating system and apps are up to date. This is because developers keep on improving applications and adding security patches which make it difficult for hackers to hack your phone.
Beware of phishing emails
Avoid clicking on suspicious links and promotional emails. Clicking these links is a way to give access to hackers who can obtain your personal information.
Having a strong password
You are encouraged to use a strong password or use fingerprint or face unlock to protect your phone from intruders. Spyware is physically placed on your phone and having a password will stop criminals from planting the app on your phone. Passwords are also important in cases where your phone gets lost; it will stop the first person to pick your phone from accessing your documents.
In conclusion
The truth is that it’s not possible to completely eliminate hacking. The best protection is ensuring that your service stays up to date, your personal information like your number is not in the public domain, and that you avoid using public wifi.
We build apps with all the security features at their core. If you are looking to build an app, then look no further. Talk to us today.